google chrome
Google Drive Now Automatically Syncs Files for Offline Editing

Chrome: Google Drive has had offline access to files for a little while, but the process wasn't automatic. With a recent update that's rolling out to users today, all your Google Drive files that you create will automatically be stored for offline access.
- Add new comment
- Read more
- 3893 reads
- Feed: Lifehacker: Google Chrome
Penny Pinching in the Cloud: How to run a two day Virtual Conference for $10
We've just finished Day One of "" our community-run free online conference for developers who love the .NET development platform and open source!
The Conference Platform
It seems funny to call the software our conference runs on a "platform" as that sounds very "enterprisey" and official. In the past we've done and with sponsors who helped pay for things. We used Channel 9 and had a studio and streamed either from Seattle or using Live Meeting.
However, this year we wanted to do it on the cheap and more distributed. We wanted speakers from ALL over in all time zones. How cheap? About USD$10ish we figure. I'll get a complete bill later, but we basically wanted to scale up, do the talks and scale down.
- Add new comment
- Read more
- 3971 reads
- Feed: Scott Hanselman's Computer Zen
Project-less scripted C# with ScriptCS and Roslyn
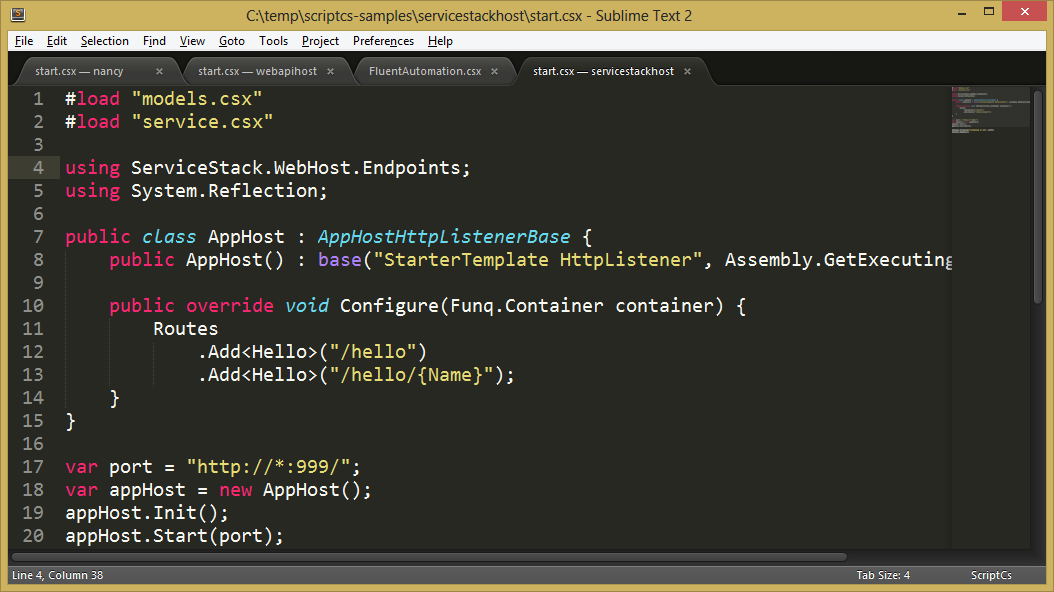
is working on something interesting that combines C#, NuGet, Roslyn (the new "compiler as a service") and his love of text editors and scripts. Now, with help from Justin Rusbatch () and Filip Wojcieszyn () they are having all kinds of fun...using C# as a scripting language.
- Add new comment
- Read more
- 7191 reads
- Feed: Scott Hanselman's Computer Zen
Exposed: A Blog Comment Spammer's Source Template
I've been getting a LOT of Blog Comment Spam lately, just in the at two weeks. I run all my comments through the , and I pay for it. However, this particular flavor of spam has been making it through consistently. It has a pattern, through, and I'd been trying to figure it out when this LARGE comment showed up.
Apparently while they were messing about trying to spam me, they posted their entire source template.
I'm embedding it below as a Gist, rather than copy/pasting it into my blog engine. It's so spammy, I'd hate to get delisted from Google looking rather like a splog.
Note .
One fellow says
"I used to do comment spam and this is not the most advanced one."
Really? Does one put Comment Spammer on their resume?
Another comment says that we're hating on spammers. We should embrace them because:
- Add new comment
- Read more
- 243 reads
- Feed: Scott Hanselman's Computer Zen
Penny Pinching Video: Moving my Website's Images to the Azure CDN (and using a custom domain)
I talked about last week when I added jQuery lazy loading to . Next, I (in fact, they should have always been together!). Now, I'm moving all my show images to the Azure CDN. There's been ~370 shows, and if someone visits the archives page and scrolls around it's about 8 megs of pics.
- Add new comment
- Read more
- 129 reads
- Feed: Scott Hanselman's Computer Zen
Setting up Two-Factor Authentication for your Google account AND Microsoft account

I use Two-Factor Authentication for my Google Apps account and I use the Google Authenticator application on my iPhone to generate the second factor.
Microsoft Accounts (formerly Live Accounts) just launched Two-Factor Auth and you should set it up now. That means SkyDrive, Outlook.com/Hotmail as well as the Windows Azure Dashboard can now be fronted by two-factor auth.
If you already use two-factor for Google, you can ADD your Microsoft account to the Google Authenticator application on your Android or iPhone. That means I can use one Authenticator application for all accounts which is extremely convenient.
The process for setting up two step authentication on a Microsoft account is:
- Add new comment
- Read more
- 129 reads
- Feed: Scott Hanselman's Computer Zen
Penny Pinching Video: Moving an Azure Website between data centers
I talked about last week when I added jQuery lazy loading to . I wanted to avoid paying any unnecessary bandwidth costs. The result was great and I'll be under my bandwidth this month.
I'm continuing to look for ways to optimize and pinch pennies in the cloud. I realized recently that while my Website was running in the West US Azure datacenter, the database (managed by ) was running in North Central US. This means I was paying for the bandwidth of my database calls. Not to mention, it was slower, not the best idea, plus I was calling into a SQL Server over the open internet (although I had opened the firewall to do so).
- Add new comment
- Read more
- 133 reads
- Feed: Scott Hanselman's Computer Zen
Installing Helvetica Neue Fonts with Google Chrome on Windows considered harmful
A few days ago, I visited the Xamarin.com website and noticed this. The word "Pricing" looks like "Prioing."
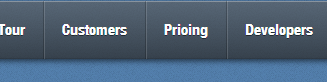
It's not an illusion. It looks wrong in Google Chrome. See this zoomed-in shot.
Here's the same menu in IE. Note the subtle"bites" that have been taken out of the g and s, but the c is OK. The hinting is OK, but the font is somehow "wrong."
- Add new comment
- Read more
- 139 reads
- Feed: Scott Hanselman's Computer Zen
How to disable the On-Screen Touch Keyboard in Windows 8
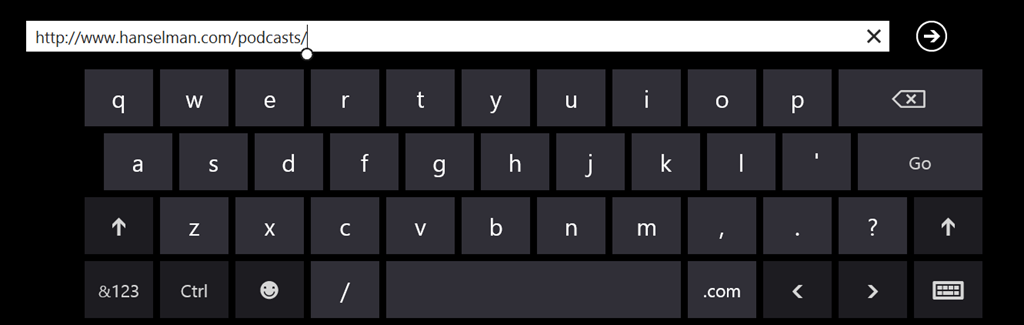
It's lovely, isn't it. It's the Windows 8 on-screen keyboard, except I don't need or want to see it. I have a Lenovo X1 Carbon Touch and it already has a keyboard. I will never ever want to use the Windows 8 touch keyboard. Unfortunately there is no checkbox or "just turn it off" way to disable the keyboard with a supported option.
However, there is a way to effectively disable the keyboard by stopping the service that controls it.
- Add new comment
- Read more
- 280 reads
- Feed: Scott Hanselman's Computer Zen
Hanselman's Newsletter of Wonderful Things: April 3rd, 2013
I have a "whenever I get around to doing it" . Why a newsletter? I dunno. It seems more personal somehow. Fight me.
You can . You can sign up here or just wait and get them later on the blog, which . Email folks get it first!
Here's the MOST RECENT newsletter, delay-posted as I do.
Hi Interfriends,
Thanks again for signing up for this experiment. Here's some interesting things I've come upon this week. If you forwarded this (or if it was forwarded to you) a reminder: You can sign up at and the .
- Add new comment
- Read more
- 122 reads
- Feed: Scott Hanselman's Computer Zen
Windows task manager shows wrong CPU Speed when using Hyper-V
My buddy Damian and I both recently bought the Lenovo X1 Carbon Touch. It's got Intel SpeedStep technology so it changes the CPU speed dynamically based on load. These two laptops of ours are identical. However, here's Damian's Task Manager when mostly idle.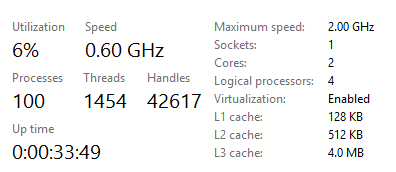
Here's mine.
_3.png)
What the heck is going on? His CPU is reporting 0.60 GHz of a potential speed of 2GHz, indicating that the chip has chilled out. Mine is reporting "full speed ahead!" at a speed that it doesn't even support, 2.49GHz!
We went around and around on this for a while until we realized that I had turned on Hyper-V Virtualization for Windows Phone Development and my Ubuntu VM. He hadn't.
- Add new comment
- Read more
- 549 reads
- Feed: Scott Hanselman's Computer Zen
Streaming Diagnostics Trace Logging from the Azure Command Line (plus Glimpse!)
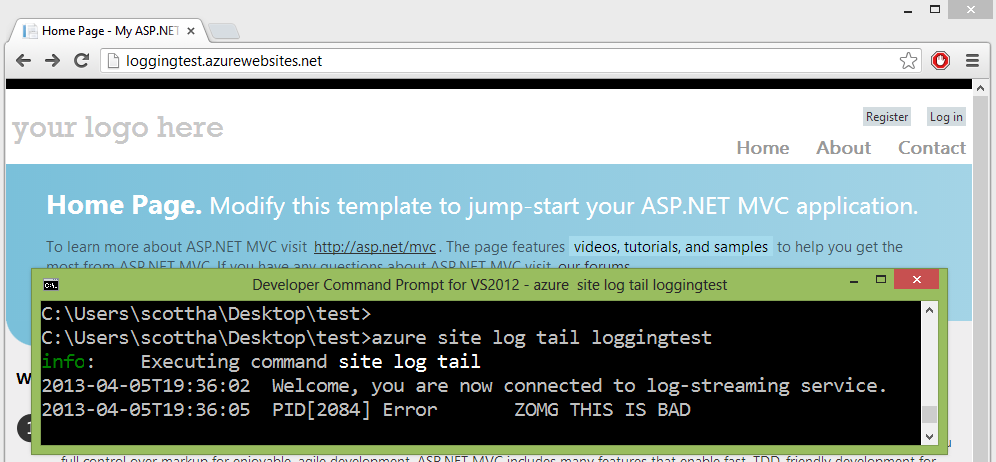
I’ve long said . Sometimes "got here"-debugging is a great tool. I tend to use System.Diagnostics.Trace a lot in my code. Then I'll use or to get more insight.
Lately though, I've been and have been wanting to get at trace data, sometimes at the .
I'll do this to deploy (or deploy from Visual Studio):
- Add new comment
- Read more
- 3556 reads
- Feed: Scott Hanselman's Computer Zen
Chrome 27 Beta: A Speedier Web and New HTML5 Forms
Today we launched Chrome 27 on the . This release introduces smarter behind-the-scenes resource scheduling and a few new features for web developers. Unless otherwise noted, updates apply to desktop versions of Chrome and Chrome for Android.
Faster page loads
Web content now appears on screen (on average) thanks to changes in Chrome’s resource scheduler. Starting with this release, the scheduler is more aggressive about using an idle connection and demoting the priority of preloaded resources so that they don’t interfere with critical assets. We’ve also added values from webpagetest.org to the list of metrics we use to measure improvements in page load time.
Elegant HTML5 date and time forms
The month, week, and date types now feature a simple, elegant user interface on desktop versions of Chrome, as shown in these screenshots from the datalist demo page:
- Add new comment
- Read more
- 78 reads
- Feed: Chromium Blog
- Original article
Blink: A rendering engine for the Chromium project
WebKit is a lightweight yet powerful rendering engine that emerged out of KHTML in 2001. Its flexibility, performance and thoughtful design made it the obvious choice for Chromium's rendering engine back when we started. Thanks to the hard work by all in the community, WebKit has thrived and kept pace with the web platform’s growing capabilities since then.
However, Chromium uses a different multi-process architecture than other WebKit-based browsers, and supporting multiple architectures over the years has led to increasing complexity for both the WebKit and Chromium projects. This has slowed down the collective pace of innovation - so today, we are introducing Blink, a new open source rendering engine based on WebKit.
This was not an easy decision. We know that the introduction of a new rendering engine can have significant implications for the web. Nevertheless, we believe that having multiple rendering engines—similar to having multiple browsers—will spur innovation and over time improve the health of the entire open web ecosystem.
- Add new comment
- Read more
- 216 reads
- Feed: Chromium Blog
- Original article
Discover Chrome DevTools - Our new interactive course
Today, we are launching Discover DevTools, an interactive Code School training course that will teach you how to take advantage of Chrome DevTool's powerful suite of resources and speed up the development and debugging of your web apps.
In each of the seven chapters of this interactive course, you can watch an overview video teaching you the latest techniques, and follow a series of challenges where your knowledge will be put to the test. We've integrated the Chrome DevTools themselves into the course, so as you explore the functionality within them, you'll get immediate feedback and earn points and badges.
- Add new comment
- Read more
- 76 reads
- Feed: Chromium Blog
- Original article
Pwnium 3 and Pwn2Own Results
Earlier this month at the CanSecWest security conference, the Chrome team took part in another Pwn2Own and hosted our third-edition Pwnium competition. This year’s participants once again impressed us with their talent and security prowess. We’re excited about what lessons we can learn from their work to make Chrome and Chrome OS even more secure.
At Pwnium, any winning entries, but did reserve the right to issue “partial” rewards. We’re pleased to reward $40,000 to Pinkie Pie, who submitted a plausible bug chain involving video parsing, a Linux kernel bug and a config file error. The submission included an unreliable exploit demonstrating one of the bugs. We’ve fixed most of these bugs already.
In particular, we’d like to thank Pinkie Pie for honoring the spirit of the competition by disclosing a partial exploit at the deadline, rather than holding on to bugs in lieu of an end-to-end exploit. This means that we can find fixes sooner, target new hardening measures and keep users safe.
In the parallel Pwn2Own contest, participants attacked many different browsers and plug-ins. There was a top prize on the line for Chrome, which was claimed by Nils and Jon of MWR Labs. Of the two bugs used, one bug was in Chrome code, which we fixed in 24 hours. Thankfully, recently deployed hardening measures protected Chrome OS users. The second bug was in the Windows kernel. The new Pwn2Own rules required the researcher to hand the bug and exploit over to Microsoft, so we’re delighted that the Chrome entry will make other products safer, beyond just Chrome.
While these security gatherings and live competitions are fun, we also want to highlight the ongoing Chromium Vulnerability Reward Program, which covers not only the Chrome desktop browser, but also all Chrome OS components and Chrome on mobile devices. We’ve given away more than $900,000 in rewards over the years and we’re itching to give more, as engaging the security community is one of the best ways to keep all Internet users safe.
- Add new comment
- Read more
- 689 reads
- Feed: Chromium Blog
- Original article
Google Chrome & Firefox Have More Vulnerabilities Than Flash And Java Combined
Time to go back to IE? Now here is something you won’t hear that often. Despite the common hate for Adobe’s Flash and Oracle’s Java plugins, it looks like they are not the major offenders when it comes to the actual number of vulnerabilities. According to the latest report by security firm Secunia, Google Chrome, [...]
- Add new comment
- 1002 reads
- Feed: Web Browsers News and Reviews
February, 2013 Desktop Market Share: Internet Explorer, Firefox, Safari, Opera Up; Google Chrome Down
If yesterday’s mobile browsers data is not exactly your cup of tea then we have another solution for you and it’s all about the desktop. As you might have guessed from the title, February was a pretty interesting month indeed. Starting off with Internet Explorer, Microsoft’s web browser continues to rebound its losses, up from [...]
- Add new comment
- 745 reads
- Feed: Web Browsers News and Reviews
Technology fails in film are the new Wilhelm Scream
There's no other explanation. It must be a tradition like the .
- Add new comment
- Read more
- 153 reads
- Feed: Scott Hanselman's Computer Zen
Our first year. A new web conference -
There's a new web conference happening in Vegas next month and you should join us. John Papa, myself and our friends pulled in the speakers from a combination of invitations and submitted talks. It's called and I hope to see you there.
My friends and I miss the old Mix conference and the great fun of web conferences in Vegas generally. So we talked to Richard Campbell and some friends and made our own show. (This is not a Microsoft show, to be clear)
- Add new comment
- Read more
- 148 reads
- Feed: Scott Hanselman's Computer Zen
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- …
- next ›
- last »
